Application Protection
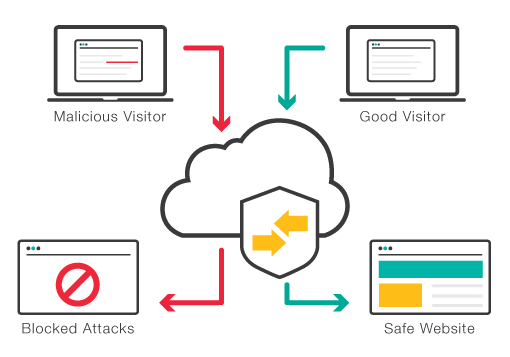
To protect you from these threats, we use Web Application Firewalls (WAFs). This protection mechanism is placed between web applications themselves and the Internet. This prevents direct access to systems and controls any interaction taking place within web app.
Protection from A to Z
Whether web shop or news portal: Web applications are becoming more and more the target of attacks from the Internet. Due to insecure and faulty programming, or system components that are no longer supported, confidential and sensitive information is being exposed to countless attack possibilities. Hackers use automated tools to steal data, resell it or blackmail affected companies. The attackers use methods that specifically exploit potential weaknesses in the web application software. The tendency is that these vulnerabilities are being totally missed or not sufficiently flagged by classic IT security systems, such as network firewalls or IDS/IPS systems – again, we have you covered.
Efficient Protection
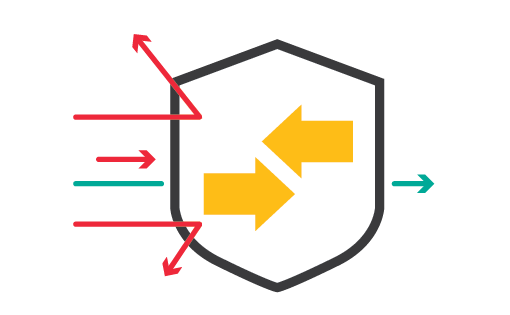
A protective wall at the application level between the business function and its interaction on the Web is situated directly in the data center. As a result, web applications themselves are no longer directly accessible and the systems and databases behind them can no longer be attacked. More to the point, every access by users and all responses from web applications are checked and blocked if necessary.
Fast Protection
It is true that with structured and security-oriented development methods, many weak points can already be avoided during the development of software or through the release of software updates. However, this simply cannot be guaranteed 100 percent. It is all too often the case that updates are a little late in closing problematic gaps or that released software is not always as secure as hoped for.
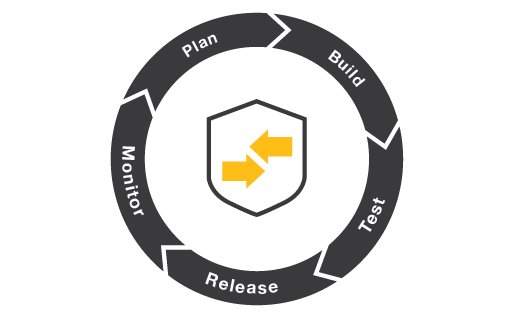
So, when protecting web applications, a combination of secure development and an upstream mechanism, that covers the entire attack surface, should always be used. For dev ops scenarios, the Web Application Firewall (WAF) integrates into such a process and can be seamlessly addressed and configured through the full API interface.
Application Protection Features
Application Attack Protection
Identity Management
REST-APIs
Compliance
Vulnerability Scanner Integration
Reporting
Application Protection Service
Clue Application Protection combines the operation of a web application firewall with the complex protection of your web applications. Our security experts create a tailor-made policy based on your requirements, advise you on the optimisation of the software code and take over the operation of the required web application firewall. This includes regular back-ups, software release and lifecycle management as well as the monitoring of health and security events. Clue Application Protection can be used flexibly on all platforms and is supported and monitored by specialists with many years of experience in the field of application security.
CLUE-less?
Bolster your team with Clue Managed Services. Our security experts are a welcome addition to your business. Proven products, tailor-made features and your very own personal support structure – we meet your requirements at a low TCO. Our monthly service fee eliminates high investments and training costs, enabling you to use our services in a modular way.